
- Check out the sneaky ways popular apps spy and gather your personal data.
- What’s the story about the U.S. banning sales of millions of Wi-Fi routers?
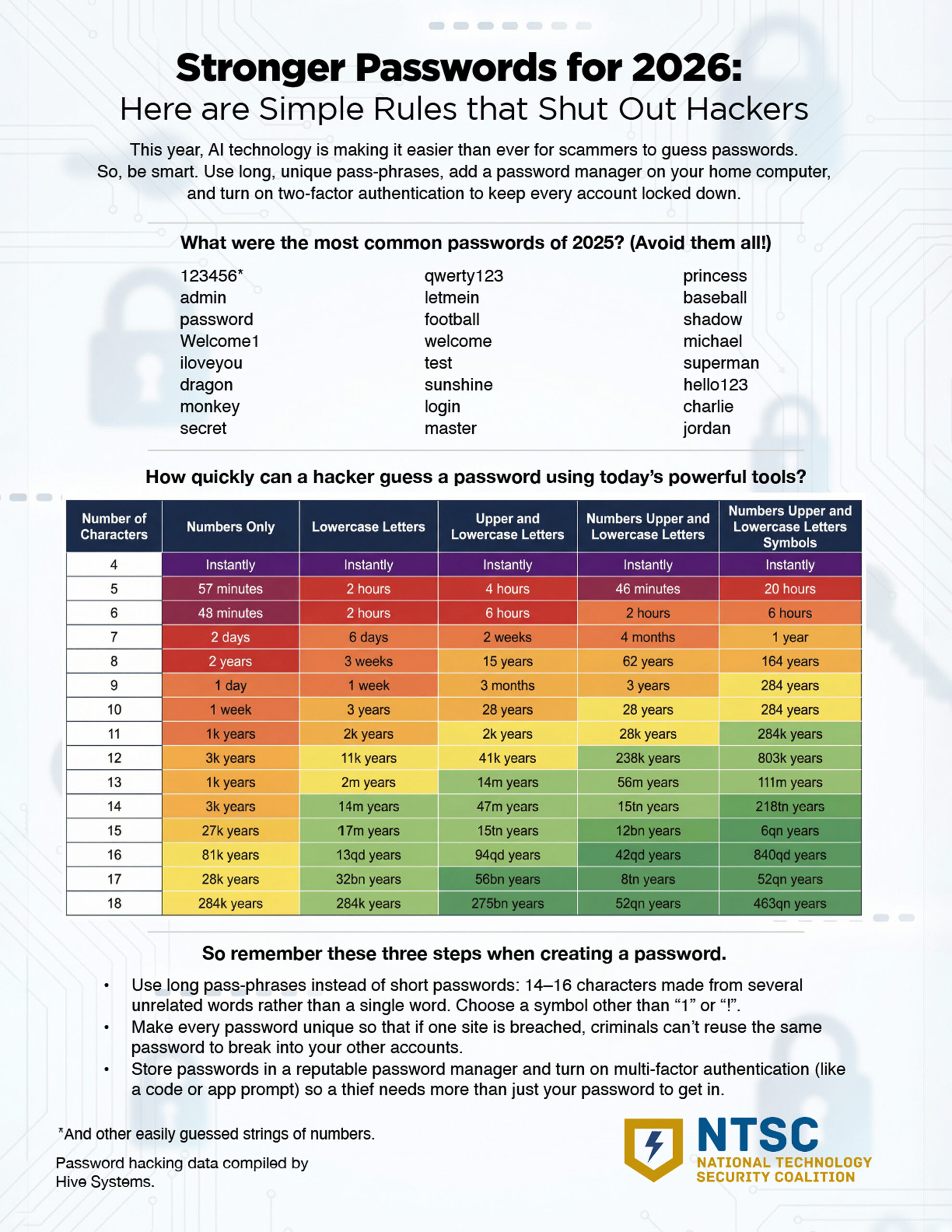
- Here’s how long is long enough for a safe password.
Live Cyber Poll
Cybersecurity News You Can Use

The U.S. government is halting the sale of foreign‑made Wi‑Fi routers because it’s worried that hostile governments are using them to spy on Americans. Your existing home router isn’t banned, but going forward, any new models made overseas will face much tougher scrutiny before they’re allowed into the country.
Once the stock of existing routers is gone, you could see shortages and price hikes as American companies establish local manufacturing and seek U.S. approval for new models.

Political ads are about to get a lot weirder, thanks to AI. In the US, a candidate’s campaign can legally show just about anything in an ad, including AI-generated versions of an opponent, and TV stations can’t legally censor it.
But outside organizations, such as political action committees that promote a candidate, are subject to much stricter rules. TV stations are free to accept or reject PAC ads, but they can be sued if they knowingly air outside‑group spots that cross into defamation, like a deepfake showing an opponent confessing to a crime they didn’t commit.
So this year, be skeptical of political ads featuring startling video or images, especially in the final weeks before an election.
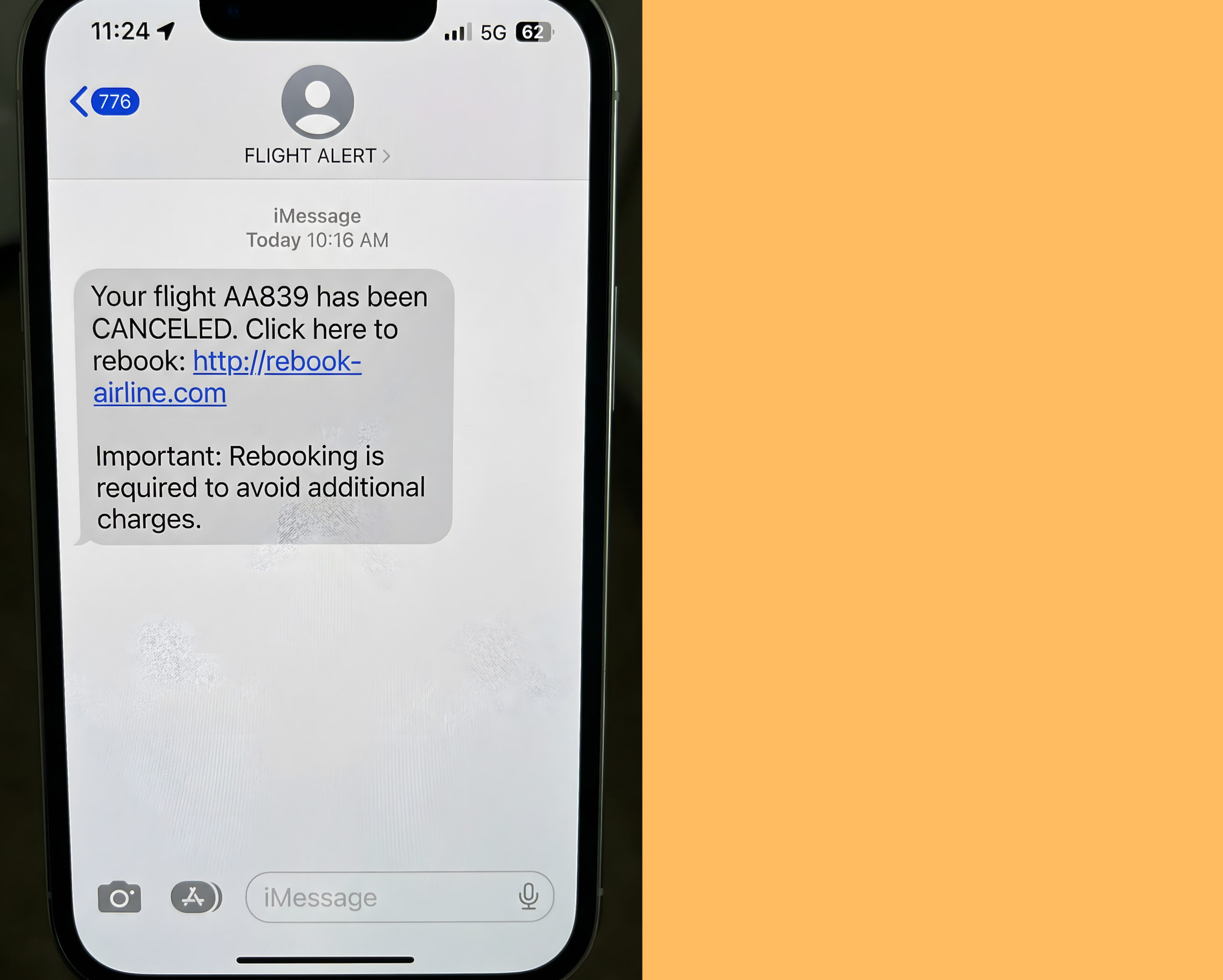
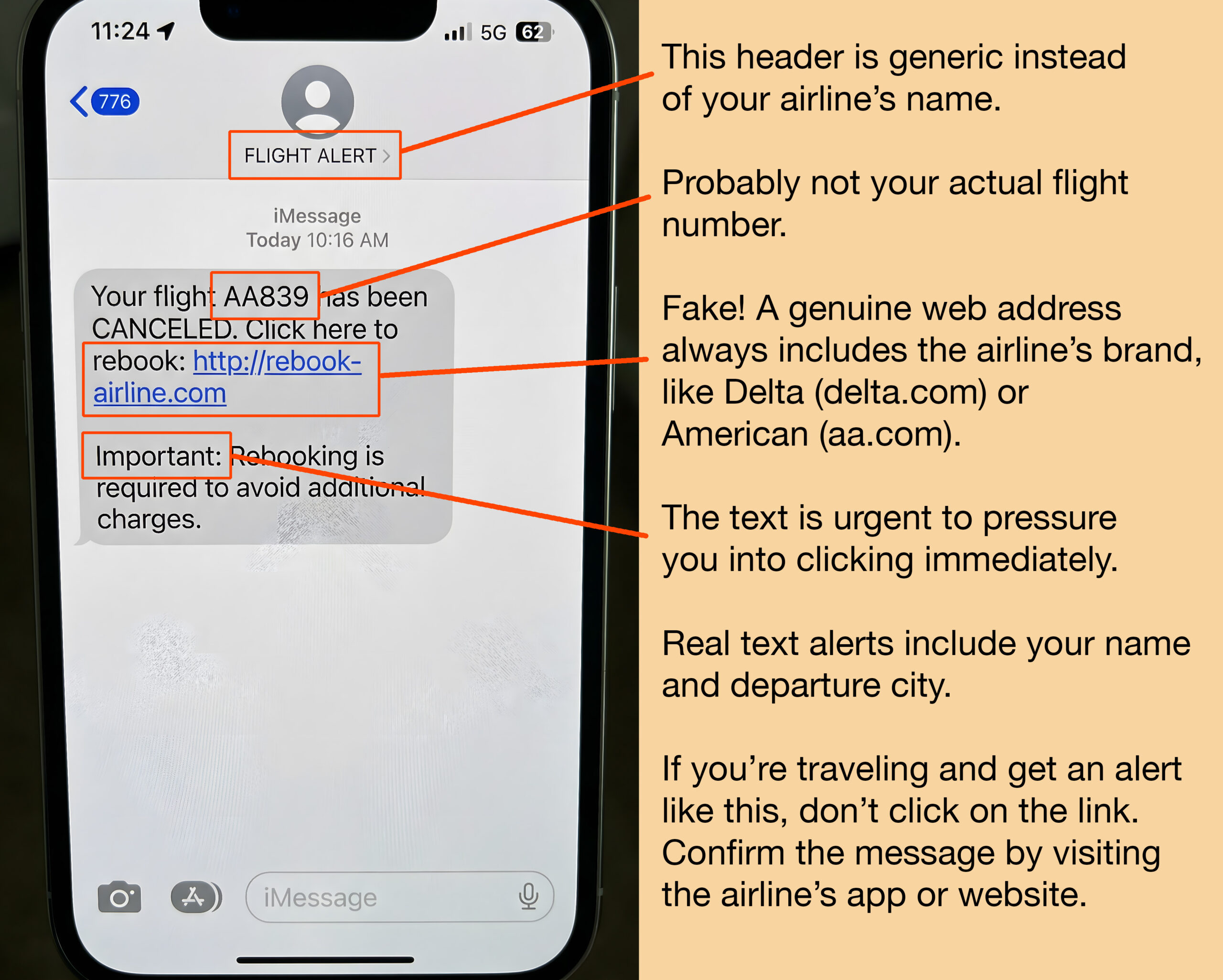
Phish of the Week
Scammers are blasting fake “flight canceled” texts during periods of airport chaos because they know stressed travelers are more likely to click without thinking.
The goal is to trick you into entering your login credentials, credit card details, or passport information on a fake rebooking site so they can steal your money and personal information.
To spot the clues: use your mouse to drag the red bar below from left to right.
One more thing...


“How do I know if my phone has been compromised, and how can we take steps to prevent it from happening?”
Great question. The most common warning signs include:
- The battery drains unusually fast. That’s because malware is running in the background and constantly burns power.
- Your phone gets hot when you’re not using it for the same reason: the processor is working overtime.
- Apps you didn’t install appear on your home screen, especially on Android.
- Strange texts or calls you never made are showing up.
- The camera or microphone light turns on by itself.
Are any of these happening to you? Turn off Wi-Fi and mobile data right away. Run a security scan using a reputable app like Malwarebytes or McAfee. Delete apps you don’t recognize and use a different device, like your home computer, to change your email, banking, and social media passwords.
Prevent this sort of mess by updating your phone’s operating system when prompted. Use a strong PIN plus fingerprint or face ID. Turn on two-factor authentication for your important accounts. And don’t connect to public Wi-Fi — that includes the network in your hotel room.
Treat your phone like your wallet.
“I just received a notice in the mail that I’m eligible for a cash settlement because my personal information was leaked when my mortgage company was hacked last year. Is this a scam? Should I fill it out? Will I qualify for a substantial amount?”
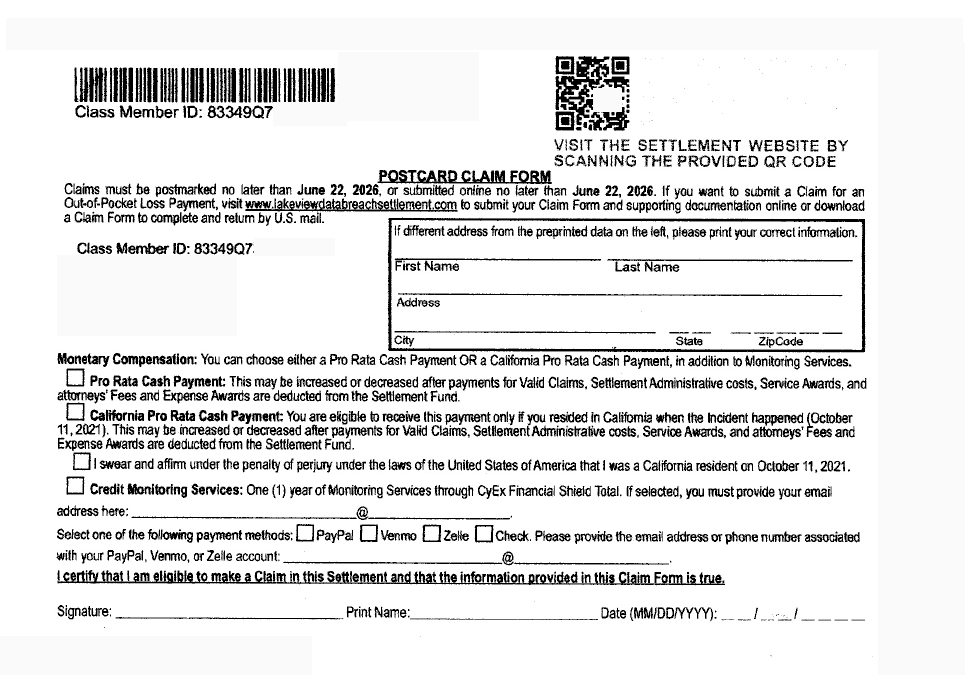
Between October 2023 and late 2025, more than 47 million Americans had sensitive financial data exposed in nine major cyber breaches. The stolen data includes some of the most sensitive financial information: Social Security numbers, bank account numbers, loan records, dates of birth, and more. So, yes, the postcard you received is legit.
You can fill it out and send it in, but don’t expect to fund your next vacation with the payout unless you suffered identity theft as a result. Most payouts might be in the $20-$40 range. Now, if you can prove you suffered financial losses, that’s a different story. The payout could be up to $5,000 — but you’ll have to prove this breach was the cause.
“Is it safe to use AI?”
ChatGPT, Claude, Perplexity, and other AI tools can be remarkably useful, but they’re not always right. A Purdue University study found that more than half of ChatGPT’s answers to programming questions contained inaccurate information. The reason: AI is designed to always produce a response, even when it doesn’t know the answer. The result is what’s known as a “hallucination,” a confident-sounding reply that’s simply made up.
There’s another layer to the problem. AI models are often trained on content scraped from social media platforms like Reddit, Facebook, and Instagram. That means the answers you receive may reflect rumors, opinions, or outright misinformation.
So, AI responses can feel authoritative, but that confidence isn’t the same as accuracy. That’s particularly important if you’re asking questions seeking personal advice.
Send us your cybersecurity question for possible use in a future newsletter.
Cyber Content Archive: Always Available
Cyber cartoon © 2026 CartoonStock | Original content © 2026 Aware Force LLC