
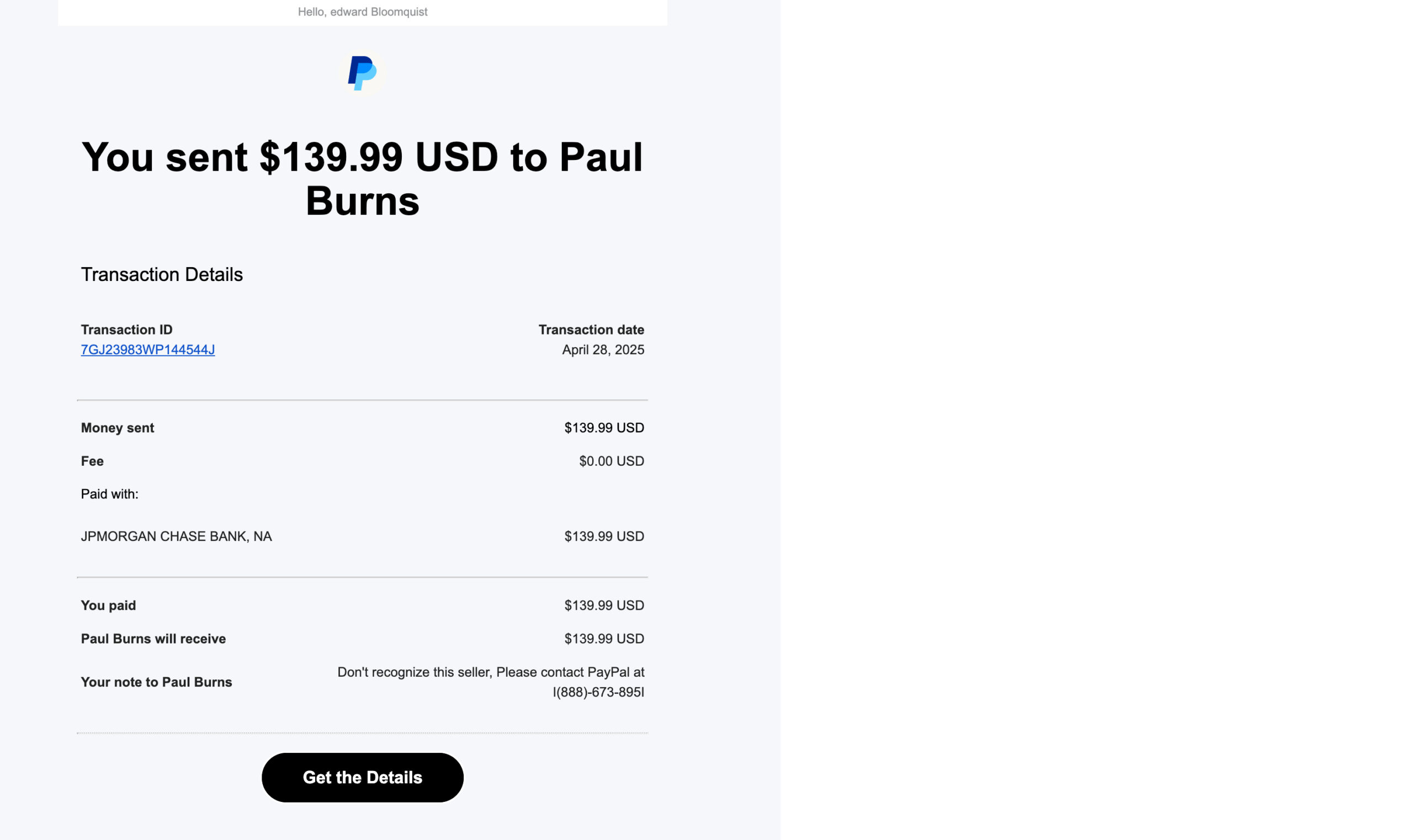
Phish of the Month
Right now, this phishing email is one of the most common — and most dangerous.
Did you really send money over PayPal
to someone you don’t know for something you didn’t buy?
Most likely, no. But scammers are hoping you’ll get mad and respond.
Use your mouse to drag the red bar from right to left and spot the clues.


WHAT’S AMISS ON WEBSITES AND HOW TO DEAL WITH IT: The ads you see on social media and popular websites are usually chosen based on what you’ve searched for or browsed online.
But the lack of robust regulation means that dangerous ads – known as “malvertising” – frequently appear on thousands of reputable websites including Disney, Fox, YouTube, Drudge, eBay, the New York Times, and even in Google search.
AdGuard says roughly 5% of these malicious ads get clicked.
Here are other sinister things we’re seeing:
Unclosable Ads:
Some ads lock your screen and push fake tech support warnings, trying to trick you into calling a toll-free number for help. Don’t respond. Quit your browser and reopen it.
Spoofed web addresses:
Ads link to websites that look just like a legitimate banking or e-commerce page—but a close look shows the web address doesn’t relate to the real thing.
Dangerous downloads:
Ads that secretly install malicious code on your computer, potentially exposing your data to criminals. Running anti-virus software on your home computer usually prevents it.
And here’s how you can better protect yourself:
Update your web browser:
When you see an alert on at the top of your browser, click “update.” Your browser will quit and relaunch, good as new.
Consider installing an ad blocker:
Reputable brands for your personal computer include uBlock Origin, Adblock Plus, Privacy Badger, and StopAd.
Report a suspicious ad:
If you encounter an unclosable ad or one that takes you to a suspicious website, report it to the website where you first saw it.

MAKE IT STOP! Robocalls are up 10% during the first half of this year, especially telemarketing calls generated by AI. We’re talking nearly 30 billion calls, in all! And if you’re getting more than your share, it could be because of what you’re doing on your social media feeds.
- If your phone number is visible on your social media profile, even just to “friends,” on your online bio, or a business post, it can be scraped and sold to spam call lists. Check LinkedIn, in particular.
- Oversharing personal details like your job, birthday, or recent purchases helps scammers craft targeted, believable calls.
- Accepting friend requests from strangers can expose your contact info to bad actors posing as real people.
- Engaging with quizzes, or “comment to win” posts can easily link your profile to scam databases.
Four steps to managing the flood of calls:
- Keep your number private. Don’t ever include it in what you post.
- Enable call-blocking features on your phone (such as “Silence Unknown Callers” on iPhone or call-blocking tools on Android).
- Consider subscribing to call-blocking apps like Hiya, RoboKiller, or Truecaller or carrier-provided solutions (like AT&T ActiveArmor, Verizon Call Filter).
- And if you get an unidentified call, let it go to voice mail.
THOSE BLACK AND WHITE SCANNABLE CODES MAY BE HIDING SOMETHING BAD: InformationWeek says 25% of all phishing emails now include QR codes because the random-looking pattern of small black and white squares can bypass even the latest email security filters.
QR codes in scam emails also target mobile users, who are less likely to spot red flags or use protective browser tools. Plus, the codes are familiar enough now that they appear to be legitimate—making users more likely to scan them without suspecting malicious intent.
One example now making the rounds: a phishing email urges recipients to scan a QR code to update their federal tax return—redirecting them to a fake Microsoft login page. Malwarebytes says the site is set up to collect victims Microsoft usernames and passwords.
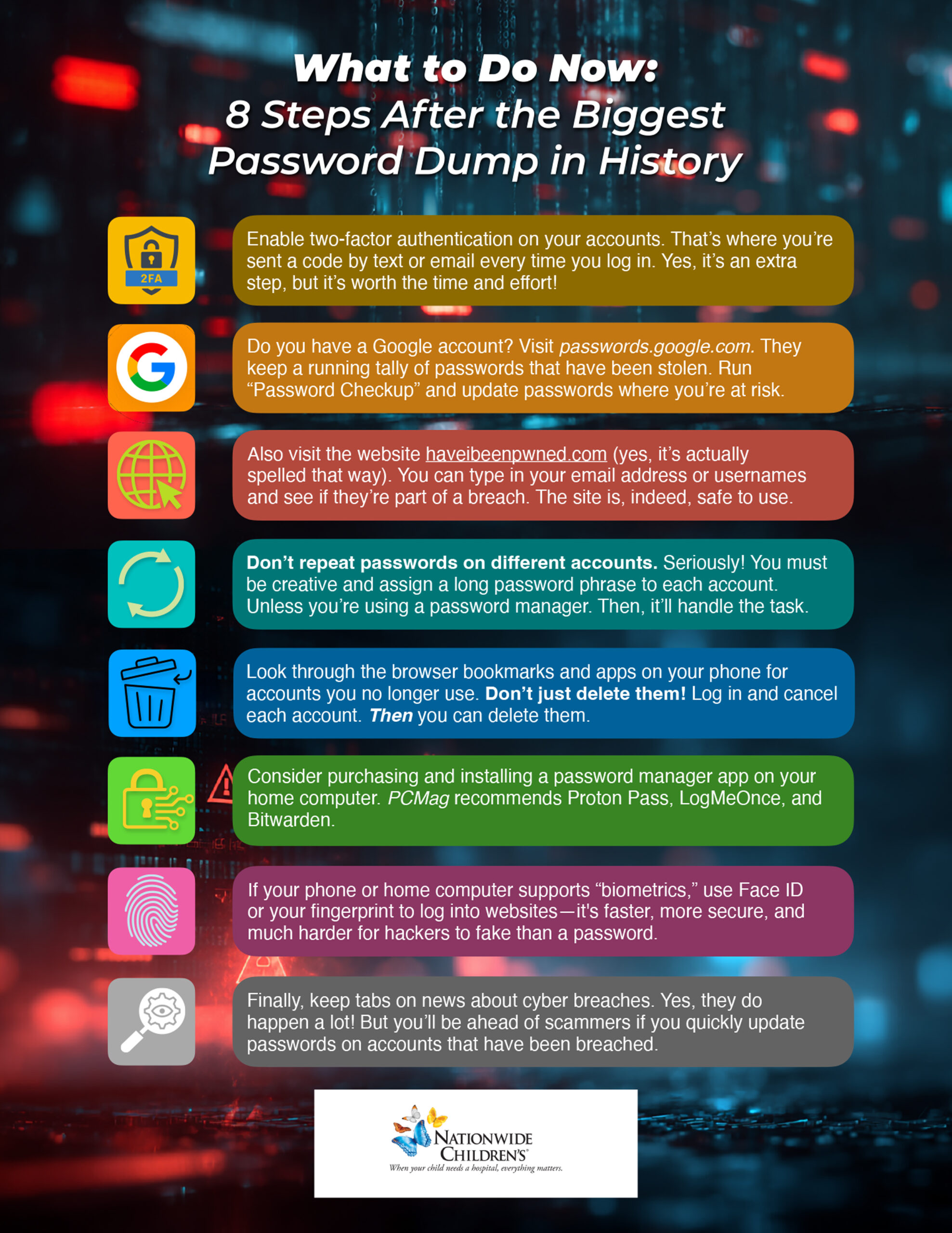
Update Your Passwords Now
These organizations say they have been hacked recently. If you do business with any of these companies, change your account password and use two-factor authentication wherever possible.




The next time you come across an outrageous post on social media, take a moment to pause and think.
Scammers are using AI to create tens of thousands of fake political accounts on platforms like Facebook, X, and LinkedIn. These accounts post provocative content designed to provoke anger and manipulate real users.
According to TheHackerNews, these campaigns often originate from foreign actors aiming to cause division, political groups trying to influence opinion, and cybercriminals testing ways to profit from engagement.
AI technology is making it easier to generate convincing, emotionally charged comments — even in native languages the scammers don’t speak, and automated tools then flood online conversations with these posts.


Have you received what you think is a fake phishing email?
Let us know right away!
The faster we know, the more we can do to protect everyone.
Click the phishing icon in your email browser to forward the suspicious email to us.
![]()
Do you have a cybersecurity question?
Here are some we’ve heard.

“I was scrolling TikTok and came across a video that showed me how to get Spotify for free. My Spidey sense told me this is a scam. Is it?”
It’s a scam, yes, and a sneaky one that is appearing quite often on TikTok feeds.
The video promises a “quick fix” to get free access to Microsoft Word, Spotify, CapCut, and other software. The video instructs you to “press Windows + R and run PowerShell commands.”
But what it really does is install malware on your computer. Ignore the instructions. Your Spidey sense is correct.
TLDR’s cyber news service reminds us to download TikTok only from official app stores. A new, dangerous version of TikTok is being promoted on websites and social media that takes screenshots of your phone as you’re using it and transmits the images to scammers.

“More and more homes and businesses have security floodlights, cameras, and ‘Ring’ doorbells. Should we assume we are always being recorded, and is our voice also being recorded for the property owner?”
Generally, yes, you’re being recorded a lot more than you might think. Ring doorbells, for example, record sound up to about 20 to 25 feet from the device. In many cases, both audio and video are saved to the owner’s account and can be reviewed by the property owner at any time.
In the U.S., laws vary by state, but in most public settings, there’s no reasonable expectation of privacy, meaning it’s generally legal to record you without your consent. Wired reports that for audio recordings, some states require two-party consent to record conversations. However, if you’re speaking loudly near someone’s property, it may still be recorded and considered lawful.
In Europe, privacy laws are tougher. To avoid capturing your neighbor’s property or public areas beyond your boundary, it is recommended that you adjust the motion and audio zones on your device.
“How do videos that put words in a person’s mouth affect security? I’ve seen video posts where you hear the person say something; the words were not their own but actually AI-generated.”
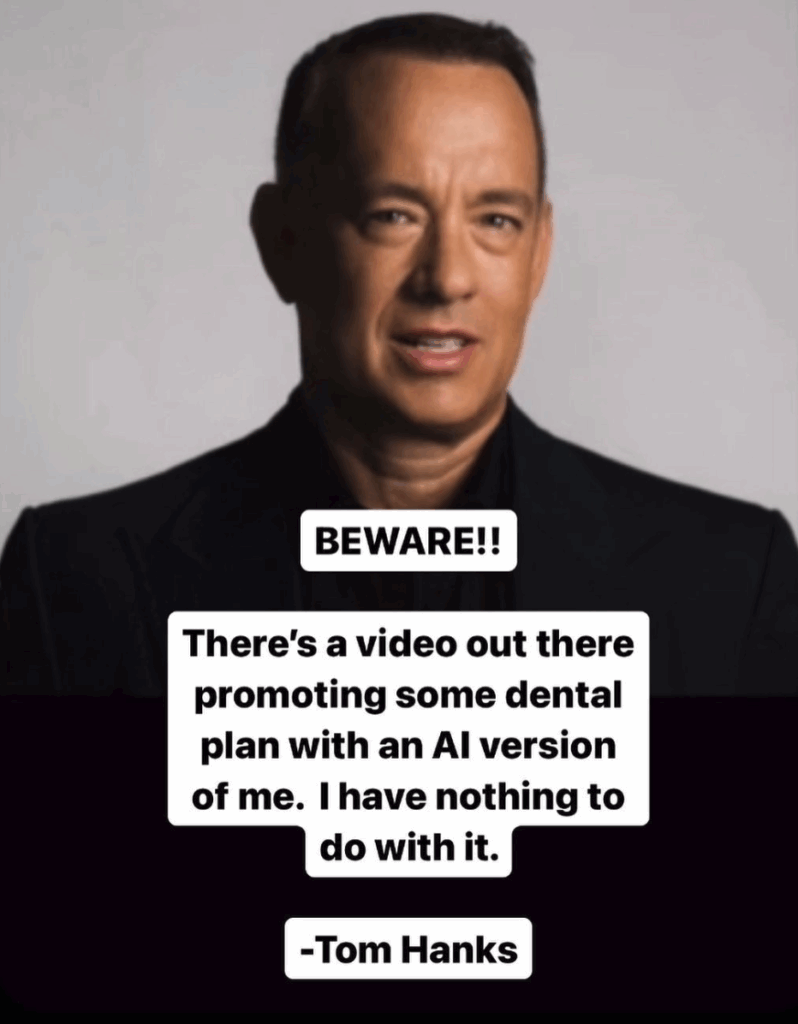
These are called “deepfakes.” As AI-generated videos become increasingly convincing, cybercriminals are using deepfakes of executives, HR reps, or family members to trick people into transferring money, divulging credentials, or installing malware on their computers.
A deepfake can also depict public figures making offensive or illegal statements, thereby damaging their reputations, careers, or public trust.
It’s only going to get worse, and unfortunately, being skeptical will be your main line of defense.
Cyber cartoon © 2025 Cartoonstock | Original content © 2025 Aware Force LLC
