

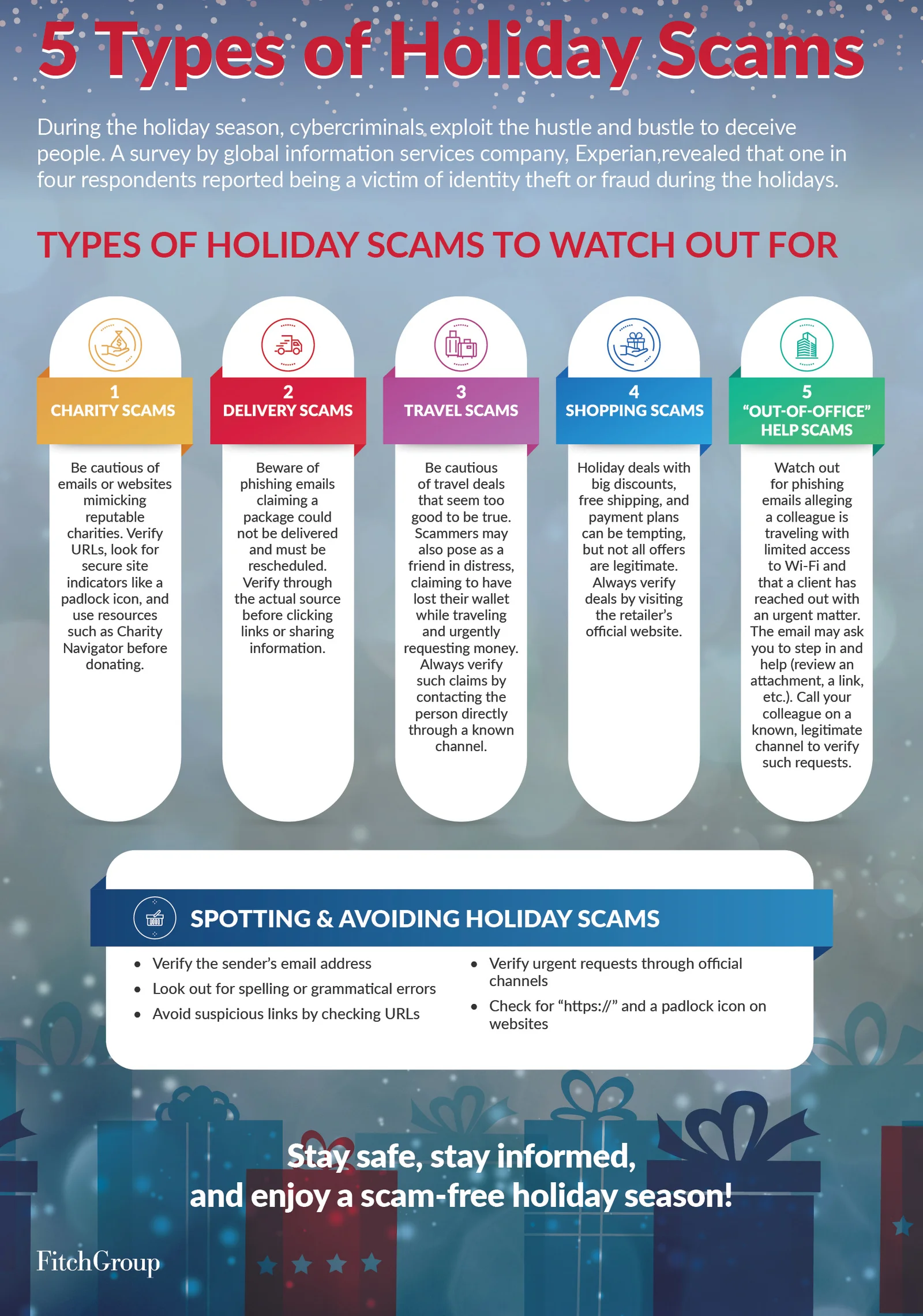
While winter holidays are a time of giving, celebration, and excitement, it’s also a time when cybercriminals are hyperactive and when people are more likely to let their guard down.
Take a look at the major holiday scams to watch out for this season. You can learn more about these scams and how to avoid them by checking out our FX article here.
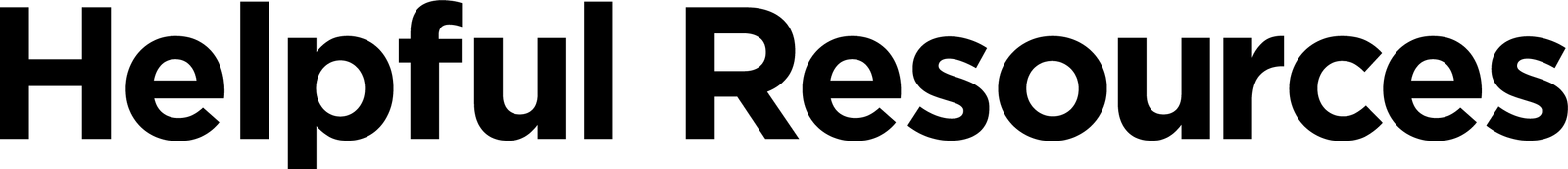
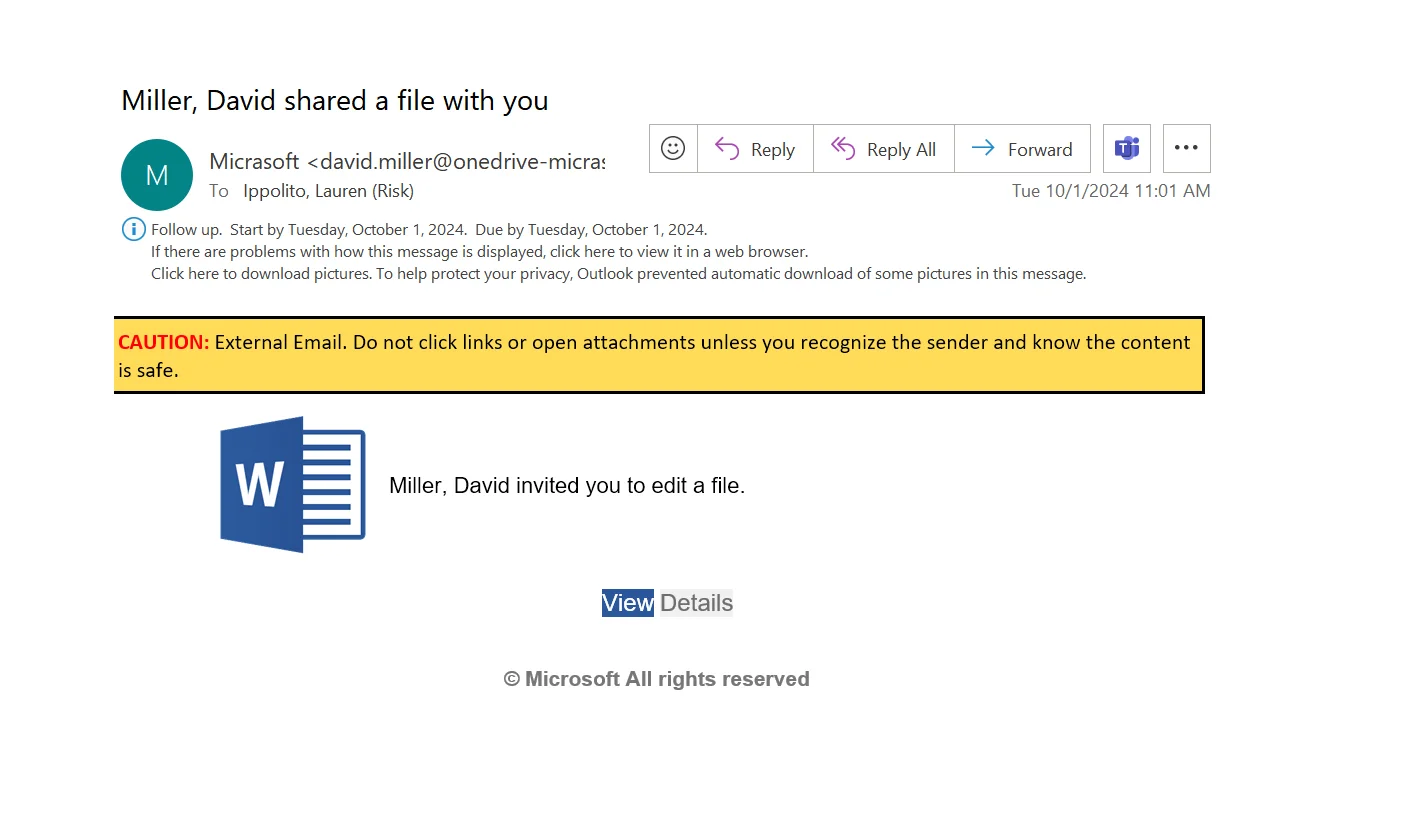
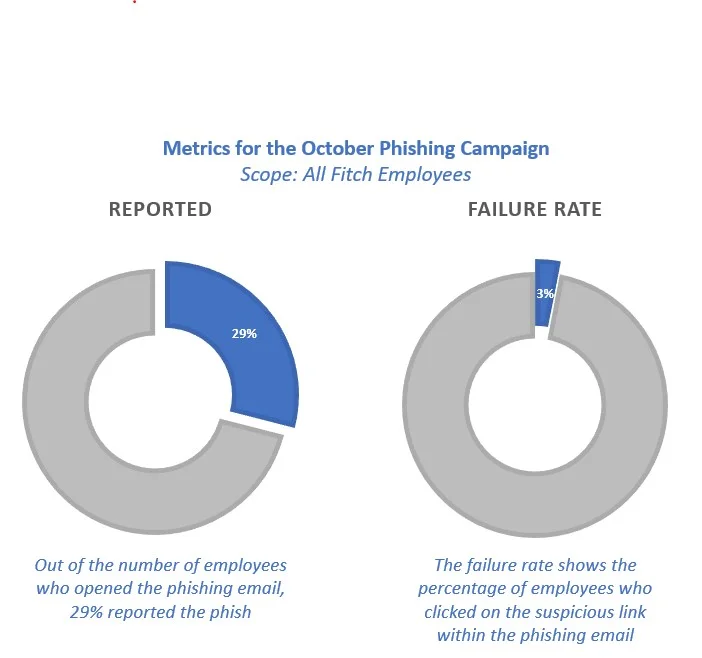
Did you catch last month’s phishing email? The October phishing campaign featured a mock Microsoft file-sharing notification. A recent study by Abnormal Security found that file-sharing phishing attacks are up over 350% in 2024. Look below to review the signs that you are being “hooked” and be on the defense for any fake file-sharing emails a cybercriminal may try to sneak into your inbox.

Phish Tank: What’s that, you ask?
Phish Tank is your go-to resource for exploring phishing examples from the Fitch phishing simulation program. These simulated phishing emails are inspired by real-world attacks designed to enhance your ability to recognize and deflect phishing attempts. Studying these examples can sharpen your skills and better protect yourself against cyber threats. Take a look here.

What percentage of cyber breaches are caused by employee errors?
According to IBM, most cyber breaches are caused by employees clicking on phishing links or sharing information in response to a text. The best advice: slow down and avoid responding immediately to urgent emails or texts, even if they seem to come from an executive.
What percentage of IT leaders have personally clicked on phishing links?
If you click on a phishing link, don’t be embarrassed—just alert IT immediately. If you accidentally entered any information on the link, be sure to change your password on the affected site right away. (Arctic Wolf)
What percentage of an organization’s revenue is lost to cyber fraud each year, on average?
Isn’t that amazing? TransUnion reports that this amounts to $359 billion in losses—based solely on data from 800 companies surveyed in the U.S., U.K., Canada, and India.
What percentage of daily emails are spam?
Emailtooltester.com reports that the most common spam email topics are prizes and giveaways, followed by job opportunities and banking.


Tell us about yourself:
I earned my master’s degree in computer science from the University of Texas at Arlington. I have always been passionate about cybersecurity, with a particular focus on application security. This enthusiasm is fueled by the growing necessity to protect sensitive data and ensure the integrity of software systems. Outside of my professional pursuits, I am an avid traveler, dancer and music enthusiast. These interests help me stay enthusiastic and effective in my profession, allowing me to tackle complex security issues with a fresh and creative mindset.
Tell us about your role:
In my role as an Associate Application Security Engineer, I am responsible for ensuring the security and integrity of our software applications. My primary focus is to ensure that security checks are part of the secure software development process. I work closely with development teams to fix any blocker that arises during these security checks. Additionally, I lead and manage the Application Security Vulnerability Management program, which involves identifying, prioritizing, and coordinating the remediation of security issues in collaboration with various squads. My role requires a combination of technical expertise, project management skills, and effective communication.
Biggest challenges you face in your role:
One of the biggest challenges I face is staying up to date with the constantly evolving landscape of cyber threats. I dedicate significant time to researching the latest vulnerabilities and remediation techniques while participating in industry events to stay informed. Despite these challenges, I remain committed to maintaining high security standards and continuously improving our processes.
Favorite thing about working in security:
My favorite thing about working in security is the dynamic and ever-evolving nature of the field. I love the challenge of tackling different threats and vulnerabilities, which requires continuous learning and adapting to new tactics used by attackers. Additionally, the opportunity to work on diverse security issues in the collaborative environment keeps my job exciting and intellectually stimulating. Ultimately, knowing that my efforts contribute to protecting our organization and its users gives me a strong sense of purpose and satisfaction.

At the beginning of November, we announced the 10 winners
of our Cybersecurity Awareness Month Scavenger Hunt.
A shout-out to all those who participated, and a special kudos to our winners!
- Bobby Lee
- Anna Eschmann
- Alex Nevling
- Michele Cuneo
- Alejandra Morales
- Adriana Bueno
- Sugath Alwis
- Mate Toth
- Minal Patel
- Richard Park

Scrolling through social media, you find a product you want to purchase.
After you enter your credit card information, you’re notified the card was declined.
Then, a short time later, you receive a text from your “bank” saying there’s a problem with your account.
You’re given a number to call. But that number doesn’t connect to your bank.
It’s the scammer’s.
They have your name, address, and card number.
And now, they want to pry more information out of you.
Lesson: If there’s a problem with your bank account, call the number on the back of your card.
Cybersecurity News You Can Use

A hacker, “Nam3L3ss,” exploited a critical vulnerability in MOVEit, a popular file transfer software, exposing sensitive employee data from over 25 major organizations. The vulnerability, CVE-2023-34362, allowed unauthorized access to bypass authentication and exfiltrate information, leading to one of the largest corporate data leaks in 2023.
The stolen data includes employee directories with names, emails, phone numbers, and cost center codes. This poses risks of phishing, identity theft, and social engineering. Companies impacted include Amazon, HSBC, MetLife, and Cardinal Health.
The breach highlights cybersecurity flaws, emphasizing the need for immediate patching, audits, and employee training. Experts warn such incidents severely impact corporate security, employee privacy, and trust.

During this year’s tax season, hackers accessed confidential data linked to H&R Block Canada, one of the country’s largest tax preparation firms. Using stolen credentials, they infiltrated hundreds of Canada Revenue Agency (CRA) accounts, altering direct deposit information, submitting fraudulent returns, and stealing over $6 million, an investigation by The Fifth Estate and Radio-Canada revealed.
Hackers fabricated addresses, including one on a non-existent “Tomato Street,” to facilitate the scam. Despite this, the CRA did not publicly disclose the breach, and Revenue Minister Marie-Claude Bibeau declined interview requests.
The CRA admitted to over 31,000 privacy breaches since 2020, affecting 62,000 taxpayers, yet it lags in reporting to Parliament. Experts, including Laval University’s André Lareau, criticize the CRA’s inability to secure taxpayer data, citing a “pay and chase” culture that prioritizes rapid refunds over fraud prevention.
These organizations say they have been hacked recently. If you do business with any of these companies, change the password on your account and use two-factor authentication wherever possible.

Want to know more?
Visit us at the Technology Risk Team FX site for helpful resources
or contact us at information.securitygroup@
to share interesting articles or suggestions for future newsletter topics.
Answers to Your
Cybersecurity Questions
Why do people scam others if it’s illegal? — Alexia S.
Mainly for the money: while individual scammers might earn a modest income, romance scammers, those who target specific employees, and ransomware criminals can steal substantial amounts from their victims. Scamming often requires little initial investment and can be done anonymously from anywhere. However, if caught, scammers can face serious consequences, including prison time, hefty fines, and the loss of any assets gained from their crimes.
Your recent video gave a tip that I should set up my child’s Social Security and IRS accounts now (before scammers do it). How do I do that? I don’t recall ever doing that for myself. — Latolander
You’re right. Setting up government accounts for a child is becoming more common. In the U.S., to establish a Social Security account for your child, start by completing Form SS-5 (available on the Social Security Administration website). You’ll need proof of your identity (such as a driver’s license) and your child’s (like a birth certificate). Submit these documents in person at a Social Security office or online through their website.
Once your child has a Social Security number, it’s a good idea to monitor their credit reports, though there likely won’t be any activity until they’re older. When your child turns 18 or begins earning income, you can set up their IRS account for managing taxes and reporting income.
How sophisticated would someone need to be to send a text that installs a tracker and accesses the microphone? — Robert M.
Gaining access to a device’s camera or microphone through a text message requires advanced technical skills. To protect your privacy, research any camera or microphone app before installing it, and only grant permissions when absolutely necessary. Norton, the security company, recommends checking your device’s small LED indicator light next to the camera — if it turns on when you’re not using a video app, it could indicate unauthorized access.
Cyber cartoon © 2024 Cartoonstock.com | Original content © 2024 Aware Force LLC