
February 2025 | 10 minute read
The Information Security Team is excited to provide its monthly newsletter,
keeping the Fitch community informed and engaged in cybersecurity.
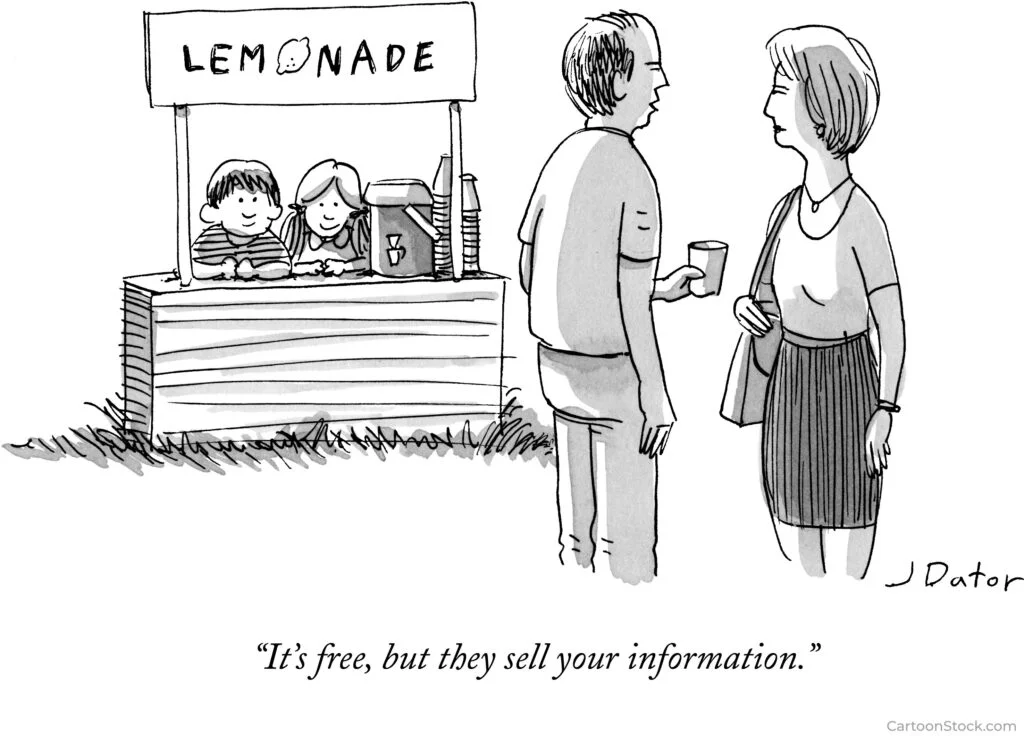
Data Privacy Awareness Week Recap
From January 21 to 24, we celebrated Fitch’s Data Privacy Awareness Week, dedicated to raising awareness about personal data collection. Our goal was to provide you with the tools to manage your personal data effectively and make informed decisions about data sharing. A heartfelt thank you to everyone who presented during the week, and we truly hope you found the events enjoyable and insightful.
Go here to read more about the Data Privacy Awareness Week recap.
Helpful Resources
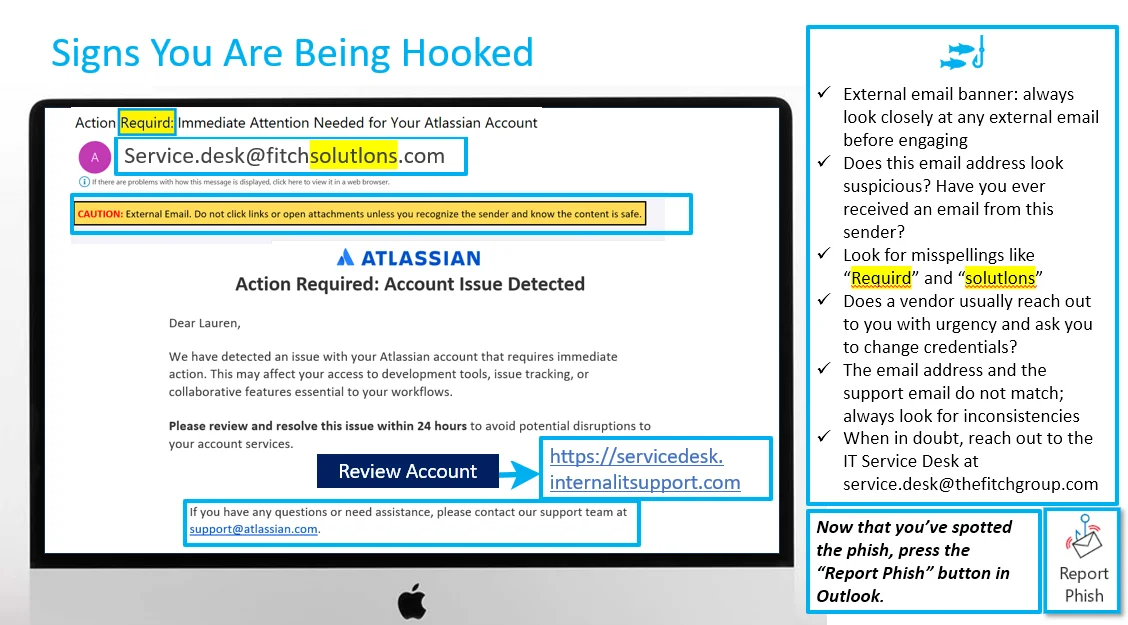
Did you catch last month’s phishing email? In January, a phishing campaign masqueraded as a fake Atlassian notification, urging recipients to verify their account details within 24 hours. This scam exploited a sense of urgency to lure recipients into entering their credentials to avoid alleged account issues. Read on to discover how to spot this tactic in the future:
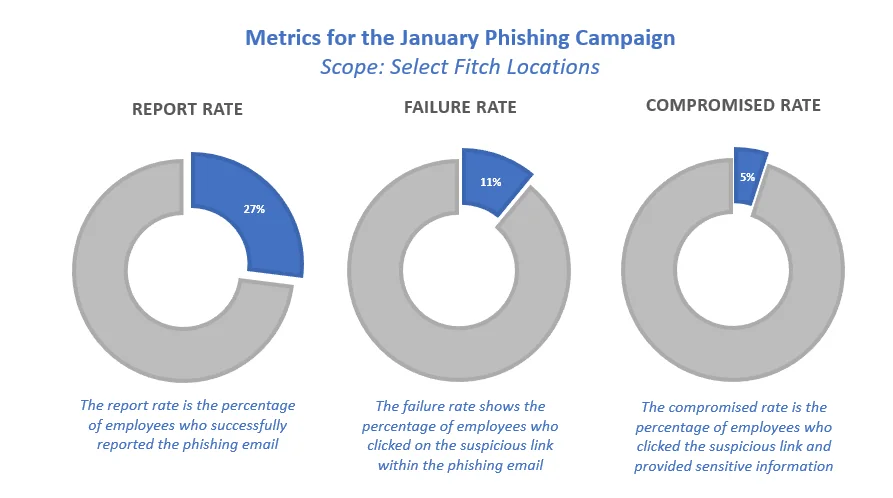
Quick Stats
Approximately 3600 Fitch employees were part of the January phishing simulation. Of this population, 27% reported the phish, 11% failed the simulation (i.e. clicked on the link), and 5% inputted their credentials. Please be assured that if you did type in your credentials, the system only records whether information was inputted. It does not record the information itself (i.e. your password).

Ready to brush up on your phish detecting skills?
Phish Tank is your essential resource for exploring phishing examples from Fitch’s simulation program. These simulations, based on real attacks, enhance your ability to recognize and deflect phishing attempts, helping you better protect against cyber threats. Explore now.
Did you receive an email that looks suspicious?
If you spot a sketchy email in your inbox, use the phishing button in Outlook. It’s a quick and easy way to keep our digital space safe and sound. By flagging these suspicious messages, you’re playing a vital role in protecting our data and avoiding harm to the company.
It’s a quick and easy way to keep our digital space safe and sound. By flagging these suspicious messages, you’re playing a vital role in protecting our data and avoiding harm to the company.
Meet the Information Security Team
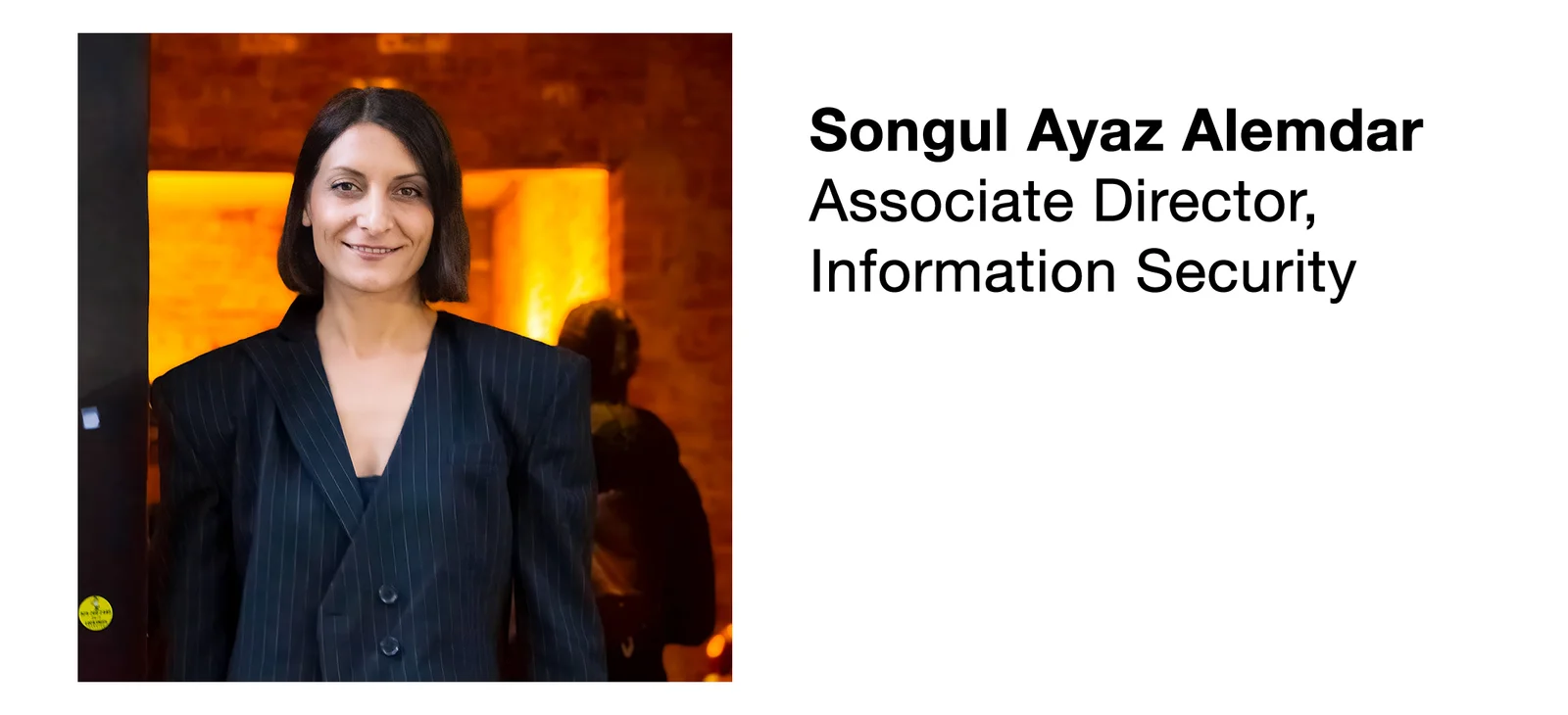
Tell us about you:
I’m a first-generation college graduate and a certified PMP, DASM, and PSM I with international experience in IT, Telecom. I specialize in program, project management governance, customer experience (CX), and strategy. I recently earned a Master of Science in IT Project Management from St. Francis College.
My profession is also my passion, I volunteer as a Board Member and VP of Programs for the Project Management Institute (PMI) New York City Chapter, where I help develop and support the project management community.
When I’m not managing projects, you’ll likely find me running, playing tennis, or cycling through Brooklyn with my 5-year-old co-pilot on our long-tail family bike.
Tell us about your role:
As a newly appointed Associate Director in the PMO within Fitch’s Information Security team, I focus on enhancing project management governance, streamlining processes, and optimizing resource allocation. I support project leads, ensuring initiatives stay on track, meet deadlines, and deliver quality results.
A key part of my role is providing strategic support to leadership, ensuring that security initiatives align with business goals. It’s a role that requires both big-picture thinking and attention to detail, and I enjoy the challenge of bringing structure to complexity and turning great ideas into real results.
Biggest challenge(s) you face in your role:
The biggest challenge is keeping the PMO evolving while ensuring project management practices remain effective as teams grow more experienced and processes become more refined. Driving change at the right pace is key, improving structure and efficiency without overwhelming teams.
Early improvements bring quick wins, but maintaining momentum and delivering long-term value requires a more strategic and adaptable approach. Fortunately, I work with a highly skilled and motivated Information Security team that makes this process seamless.
Favorite thing about working in security:
My favorite thing so far is the high visibility and collaboration that comes with being part of this team. Information Security is deeply integrated into every part of the business, working across teams protect the company’s resilience and growth.
Being part of a team that drives meaningful change across the organization makes this work especially fulfilling.
Cybersecurity News You Can Use

MASSIVE DATA BREACH OF STUDENT RECORDS: This is a big one. Parents, students, teachers, and administrators across North America are grappling with the fallout from a major data breach involving PowerSchool, a service used by 16,000 K–12 schools worldwide to manage data for 60 million students.
This breach includes Social Security numbers, medical records, home addresses, phone numbers, grades, and caregiver details for students since 2017.
Parents are urged to check for fraudulent accounts opened using their child’s information. If no credit file exists, it’s a positive sign. Parents can place a credit lock with major bureaus like Equifax and TransUnion to prevent unauthorized use, adding an extra layer of protection.

LINKEDIN SUED FOR SHARING USING USER DATA TO TRAIN AI MODELS: Some LinkedIn Premium users have filed a class-action lawsuit, alleging the platform shared their private messages with third parties to train large language models (LLMs). The suit claims LinkedIn quietly introduced a privacy setting last August, allowing users to opt in or out of data sharing. A month later, the company updated its privacy policy, stating user data could be used for AI training—while noting that opting out would not undo past data usage. The lawsuit seeks damages for breach of contract and $1,000 per person for violations of the federal Stored Communications Act.
Our recommendations:
- Select “Data Privacy,” then turn off the option under “Data for generative AI improvement.”
- Limit how much personal information you share on your profile.
- Don’t allow LinkedIn to sync your contacts.
- Turn on two-factor authentication & password verification.
- Toggle off “Advertising Data” in your profile settings.
- Turn off “share key profile updates” to avoid broadcasting your updates.
- Make yourself anonymous when looking at other profiles — Settings > Visibility > Profile viewing options.
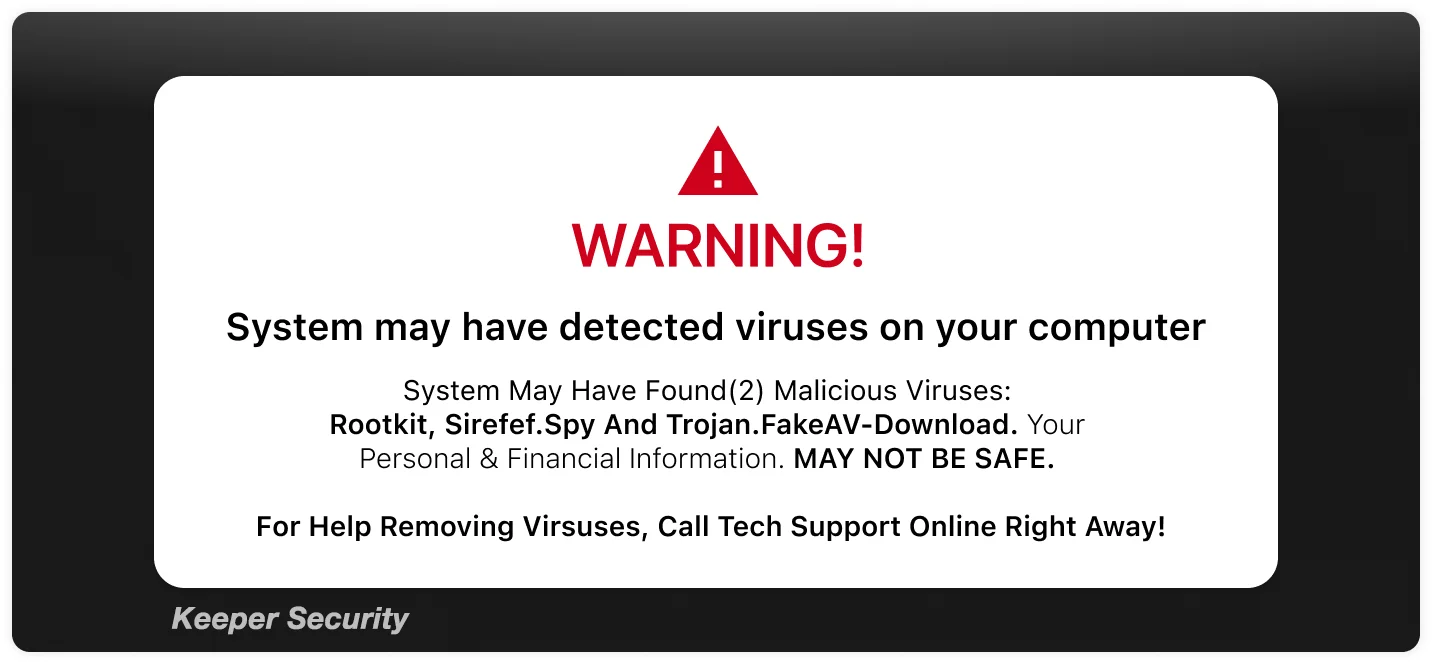
WHEN IT’S YOUR MONEY, DON’T BE SO FAST TO MOVE IT. The FBI is warning of a growing scam called “the Phantom Hacker.” According to Forbes, it begins with a pop-up ad or phishing email urging the victim to call a number about a supposed “account infiltration.” Victims are pressured to quickly move their money to “protect” it, but the transferred funds go directly to the scammer. And once the money is gone, recovery is unlikely.
Their advice: Never install an app at the direction of someone claiming to be tech support, and remember, banks will never ask for security credentials over the phone.
Want to learn more?
Visit us at the Information Security Team FX site for helpful resources
or contact us at information.securitygroup@
to share interesting articles or suggestions for future newsletter topics.
One more thing...
Answers to Your
Cybersecurity Questions
“I received an email that appeared to be from my credit card company, notifying me of a suspicious charge on my account. The email address looked legitimate, so I called the toll-free number provided. Instead of reaching a customer service representative, I was stuck listening to a recorded sales pitch for a Medicare Advantage Plan, with no option to connect to the help desk. What did I miss?” — Jackie S.
It turns out the toll-free number you called was, in fact, the credit card company’s legitimate number. However, some credit card companies have started using pre-recorded sales pitches before connecting callers to a representative. This is especially frustrating when the issue you’re calling about could indicate a potential breach of your account. To bypass the recording, try calling the number again—it should connect you directly.
“What should you do if your personal information is for sale on the dark web?” — Shundetta S
It probably is. The more active you are online—especially if you use lesser-known e-commerce sites, fall for phishing emails, or reuse passwords—the greater the chance your personal information is sold to scammers. A quick check on haveibeenpwned.com can help determine if your data has been compromised.
Companies like Norton, McAfee, Surfshark, Identity Guard, and Aura offer subscription services to monitor your credit and alert you to potential risks. It’s a good idea to research these services online to understand their pros and cons and learn how to freeze your credit to protect against fraud.
“I just saw a report on the news about someone whose house was sold without their knowledge, and they owned the house! I have a mortgage. How can I protect myself from that?” — Bendita12
This is called title fraud or property deed theft. It occurs when scammers transfer ownership of a property without the owner’s consent. Since property deeds are part of public records, fraudsters can exploit that accessibility. Although title fraud is relatively rare, it is more common in high-value real estate areas and among homeowners who own their properties outright.
To protect against this risk, many local government offices and private companies offer deed fraud alert programs, which notify property owners of any changes to their deeds. Title insurance is another valuable safeguard, protecting against potential future claims on the property. This is a one-time fee that varies by state.
Cyber cartoon © 2025 Cartoonstock | Original content © 2025 Aware Force LLC