July 2025 | 10 minute read
The Information Security Team is excited to provide its monthly newsletter,
keeping the Fitch community informed and engaged in cybersecurity.


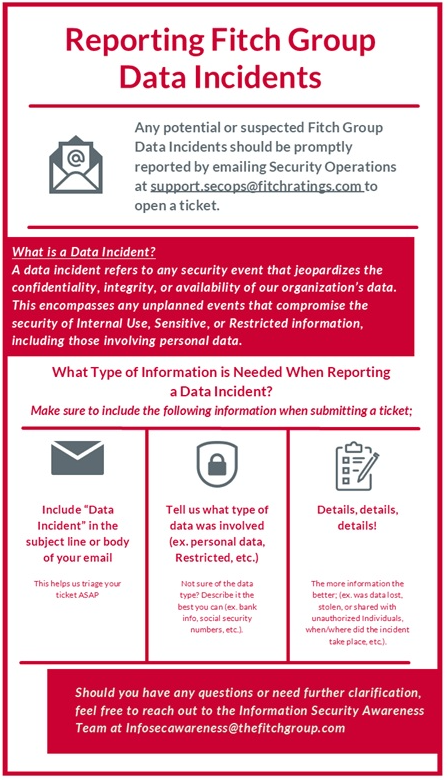
The Information Security and Security Operations teams have improved the process for reporting Fitch Group (including Fitch Ratings) data incidents.
Effective immediately, any potential or suspected data incident(s) should be promptly reported by emailing Security Operations at [email protected] to open a ticket.
Swift reporting ensures that risk is quickly mitigated and adherence to specific legal requirements for reporting data incidents.
Fitch Ratings employees: Please note that in the event of an incident or occurrence that is contrary to the requirements identified under any Fitch Ratings or Fitch Group Bulletin applicable to Fitch Ratings, you should submit a ticket in the Exceptions Management System (EMS).
Should you have any questions or need further clarification, please visit the Information Security FX page or contact the Information Security Awareness Team at [email protected].
Meet the Information Security Team
Tell us about yourself?
Hi, my name is Ahmad Yusuf. I am always excited about anything technology related, love helping people out the best I can and drawn to community activities.
What are you studying at school?
I’m currently studying Information Systems and Technology at Worcester Polytechnic Institute.
Can you share a fun or surprising fact you’ve learned about cybersecurity during your internship?
Before interning at Fitch Group, I knew that information is a powerful resource that needs to be protected. One surprising fact I’ve learned during my internship is that cybersecurity issues are purely human-driven. It’s been eye opening to see how easily information can be stolen or weaponized, whether through simple data gathering techniques or the lack of security in IoT devices. I’ve also gotten to learn about Fitch Group’s information security hierarchy and the different technologies and methodologies that play a role in keeping data safe. These insights as given me a new mindset about systems, seeing them in a sustainable way that ensures they remain safe, efficient, and resilient against bad actors, not just focusing on how they help.
Have you worked on any interesting projects or tasks so far? What did you enjoy most about them?
One of the most interesting projects I’ve worked on is creating a PowerBI dashboard for tracking the key metrics of our human risk training programs aimed at reducing cybersecurity threats. This project really pushed me to refine my skills and gain confidence, and I enjoyed the process of asking questions and receiving feedback from my managers. It made me feel like I was truly contributing to raising awareness of cybersecurity issues and strengthening our overall security posture. Additionally, these experiences are helping better understand where I want to go in the IT world and are informing my future career decisions.
What’s something you enjoy doing outside of work or school? Any hobbies or interests you’d like to share?
Outside of work, I love going to the gym, listening to music, and going for runs. These hobbies help me unwind and stay balanced.

The average person receives more than a dozen spam emails every day, most often using tactics like fake invoices, “password check required” alerts, or urgent account warnings to trick users into clicking.
While that tempting “unsubscribe” link might seem like the easiest way to stop these emails from coming, it can actually confirm your address is real. Even worse, it can take you to sophisticated scam websites.
The Wall Street Journal advises that instead of clicking links in the body of emails from unknown senders, you should use your email app’s built-in list-unsubscribe button, mark messages as spam, or set up filters.
Also, try creating a special email address for use when you’re signing up for newsletters, online promotions, and social media platforms. You’ll be shocked at how often that address gets shared with other companies.
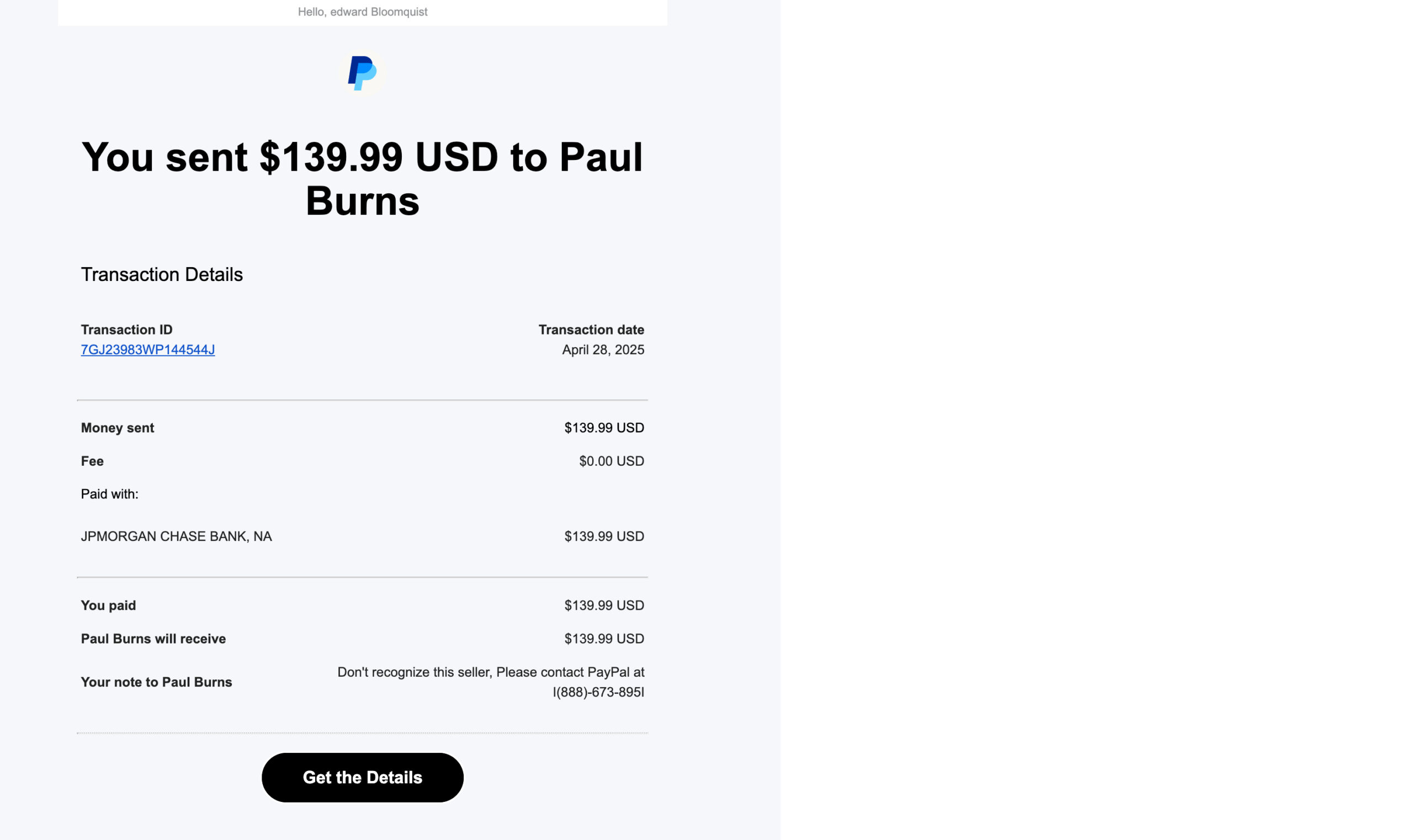
Spam of the Week
This spam email is designed to raise your blood pressure.
Did you really send money to someone you don’t know for something you didn’t buy?
Most likely, no. But scammers are hoping you’ll get mad and respond.
Use your mouse to drag the red bar from right to left and spot the clues.
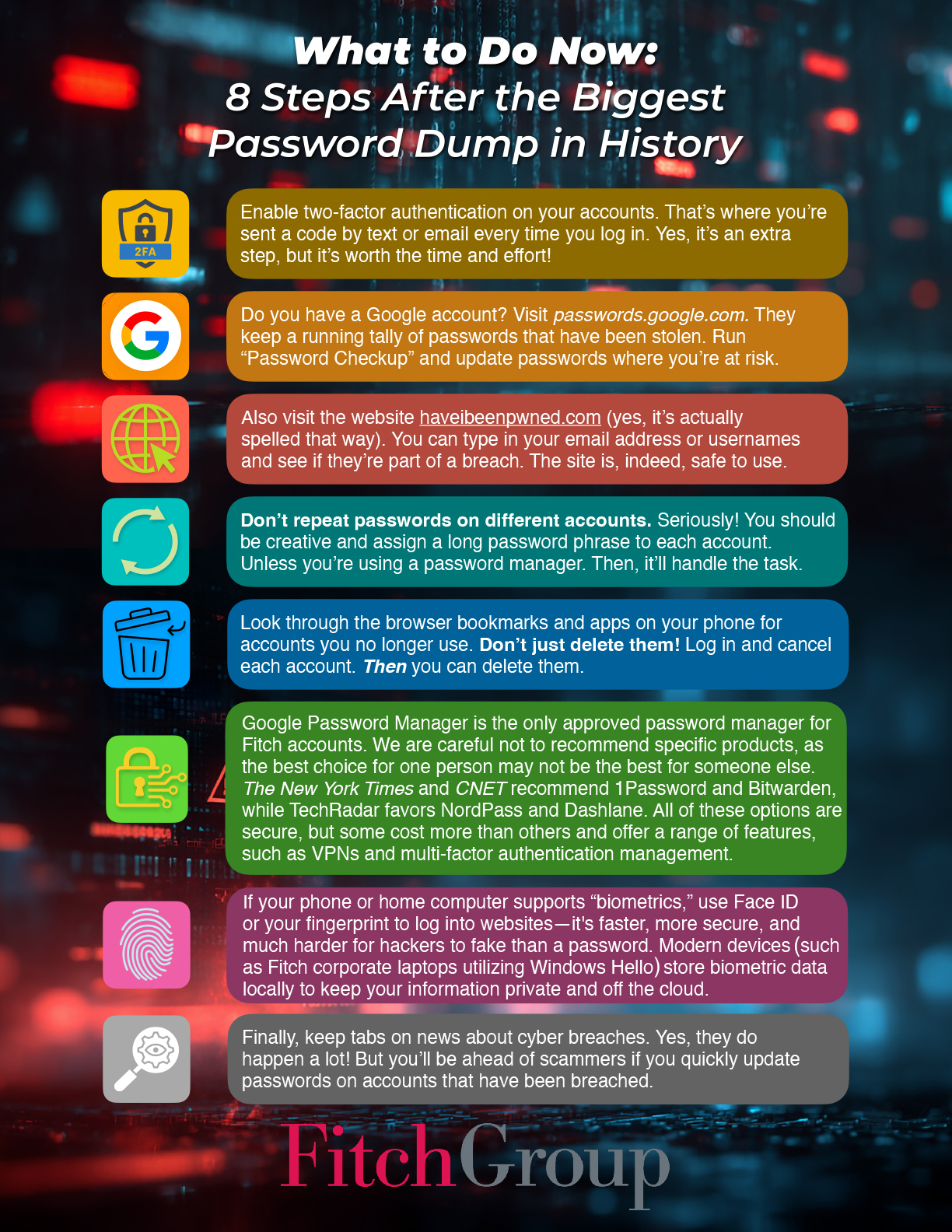
Update Your Passwords Now
These organizations say they have been hacked recently. If you do business with any of these companies, change your account password and use two-factor authentication wherever possible.

Want to learn more?
Visit us at the Information Security Team FX site for helpful resources
or contact us at information.securitygroup@
to share interesting articles or suggestions for future newsletter topics.
One more thing...

Answers to Your
Cybersecurity Questions

“I was scrolling TikTok and came across a video that showed me how to get Spotify for free. My Spidey sense told me this is a scam. Is it?”
It’s a scam, yes, and a sneaky one that is appearing quite often on TikTok feeds.
The video promises a “quick fix” to get free access to Microsoft Word, Spotify, CapCut, and other software. The video instructs you to “press Windows + R and run PowerShell commands.”
But what it really does is install malware on your computer. Ignore the instructions. Your Spidey sense is correct.
TLDR’s cyber news service reminds us to download TikTok only from official app stores. A new, dangerous version of TikTok is being promoted on websites and social media that takes screenshots of your phone as you’re using it and transmits the images to scammers.

“More and more homes and businesses have security floodlights, cameras, and ‘Ring’ doorbells. Should we assume we are always being recorded, and is our voice also being recorded for the property owner?”
Generally, yes, you’re being recorded a lot more than you might think. Ring doorbells, for example, record sound up to about 20 to 25 feet from the device. In many cases, both audio and video are saved to the owner’s account and can be reviewed by the property owner at any time.
In the U.S., laws vary by state. Video surveillance is more broadly allowed than audio in the United States. For example, recording inside someone else’s home, apartment hallway, or shared building spaces is often more restricted (you might expect some reasonable privacy in these places, even if you are someone else’s home – at least signage is expected) than front yard/street views.
Wired reports that for audio recordings, some states require two-party consent to record conversations. However, if you’re speaking loudly near someone’s property, it may still be recorded and considered lawful.
In Europe, privacy laws are tougher. To avoid capturing your neighbor’s property or public areas beyond your boundary, it is recommended that you adjust the motion and audio zones on your device.
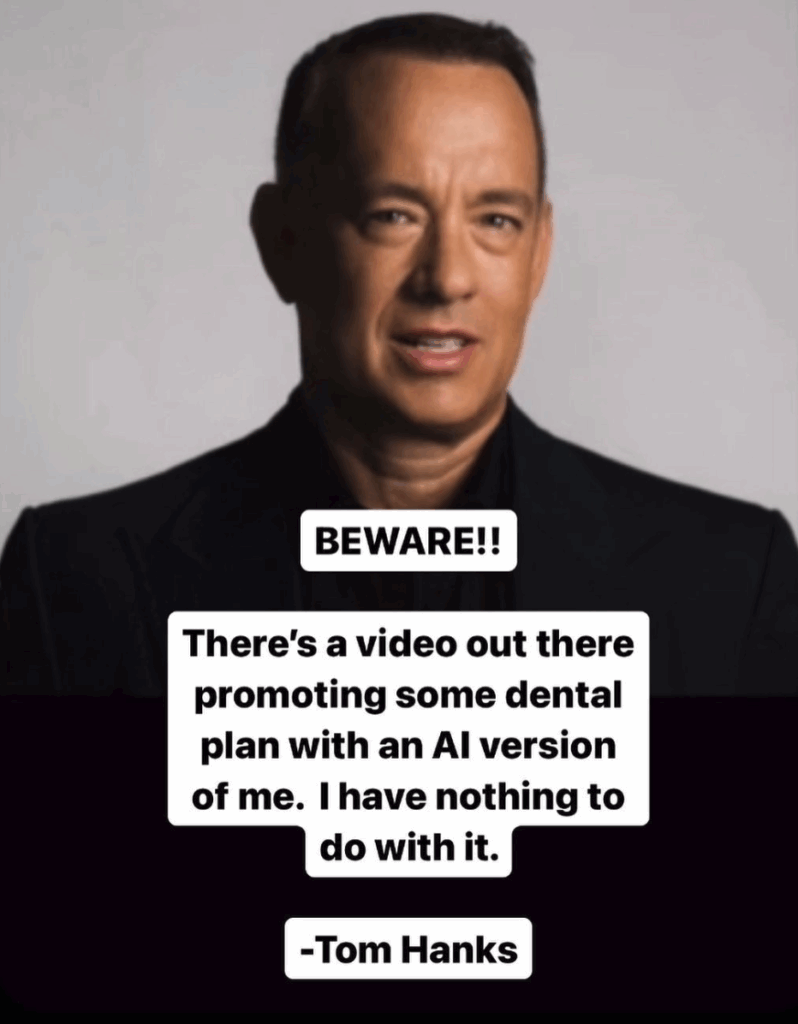
“How do videos that put words in a person’s mouth affect security? I’ve seen video posts where you hear the person say something; the words were not their own but actually AI-generated.”
These are called “deepfakes.” As AI-generated videos become increasingly convincing, cybercriminals are using deepfakes of executives, HR reps, or family members to trick people into transferring money, divulging credentials, or installing malware on their computers.
A deepfake can also depict public figures making offensive or illegal statements, thereby damaging their reputations, careers, or public trust.
It’s only going to get worse, and unfortunately, being skeptical will be your main line of defense.
Cyber cartoon © 2025 Cartoonstock | Original content © 2025 Aware Force LLC